| SA |
01 |
System and services acquisition policy and procedures |
- Develop, document, and disseminate to [Assignment: organization-defined personnel or roles]:
- [Selection (one or more): Organization-level; Mission/business process-level; System-level] system and services acquisition policy that:
- addresses purpose, scope, roles, responsibilities, management commitment, coordination among organizational entities, and compliance
- is consistent with applicable laws, Orders in Council, directives, regulations, policies, standards, and guidelines
- procedures to facilitate the implementation of the system and services acquisition policy and the associated system and services acquisition controls
- Designate an [Assignment: organization-defined official] to manage the development, documentation, and dissemination of the system and services acquisition policy and procedures.
- Review and update the current system and services acquisition:
- policy [Assignment: organization-defined frequency] and following [Assignment: organization-defined events]
- procedures [Assignment: organization-defined frequency] and following [Assignment: organization-defined events]
|
Activity |
Selected |
NA |
NA |
| SA |
02 |
Allocation of resources |
- Determine the high-level information security and privacy requirements for the system or system service in mission and business process planning.
- Determine, document, and allocate the resources required to protect the system or system service as part of the organizational capital planning and investment control process.
- Establish a discrete line item for information security and privacy in organizational programming and budgeting documentation.
|
Control |
Selected |
NA |
NA |
| SA |
03 |
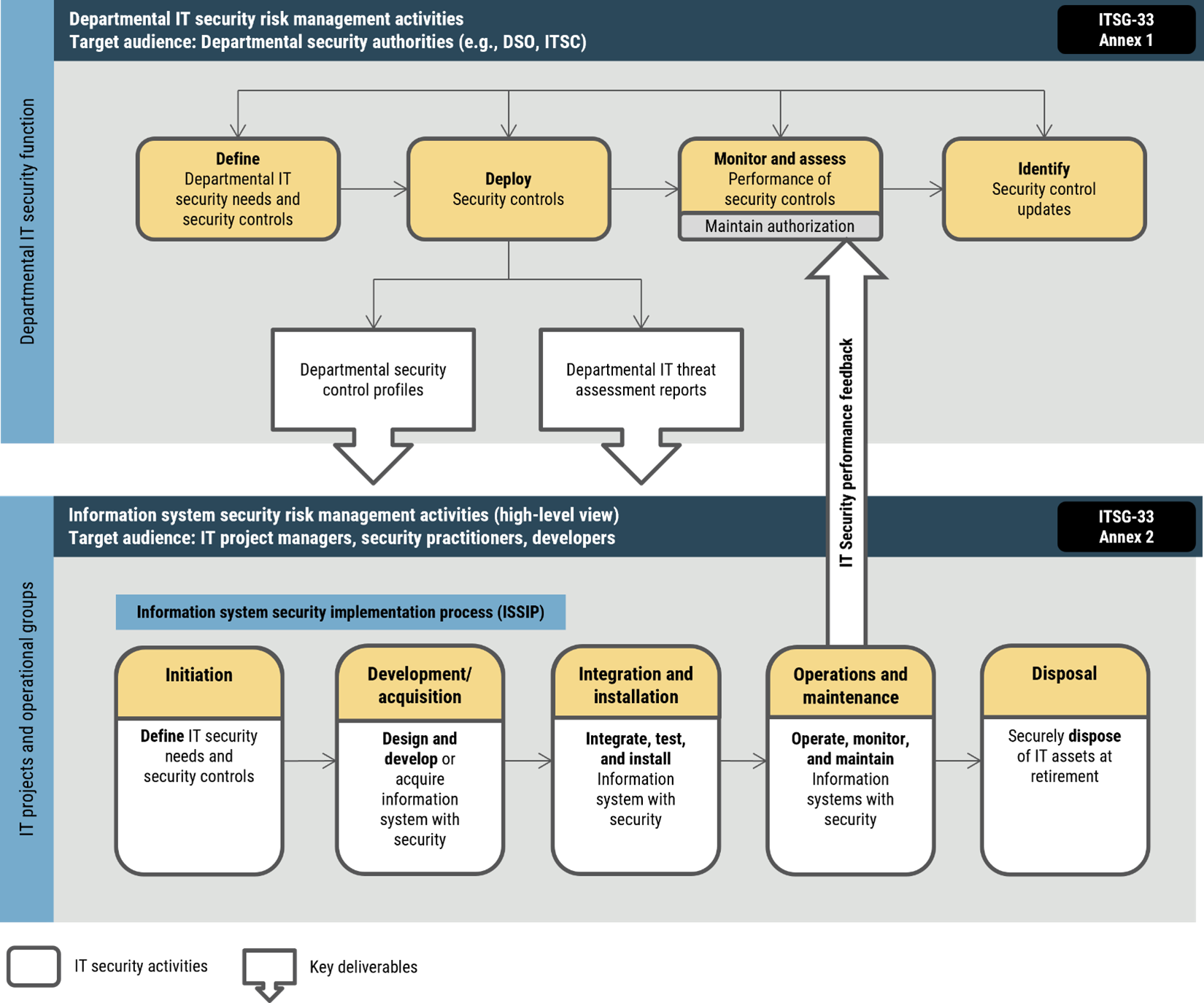
System development lifecycle |
- Acquire, develop, and manage the system using [Assignment: organization-defined system development lifecycle] that incorporates information security and privacy considerations.
- Define and document information security and privacy roles and responsibilities throughout the system development lifecycle.
- Identify individuals having information security and privacy roles and responsibilities.
- Integrate the organizational information security and privacy risk management process into system development lifecycle activities.
|
Activity |
Selected |
NA |
NA |
| SA |
03(01) |
System development lifecycle |
System development lifecycle: Manage pre-production environment
Protect system pre-production environments commensurate with risk throughout the system development lifecycle for the system, system component, or system service. |
Activity |
Not selected |
NA |
NA |
| SA |
03(02) |
System development lifecycle |
System development lifecycle: Use of live or operational data
- Approve, document, and control the use of live data in pre-production environments for the system, system component, or system service.
- Protect pre-production environments for the system, system component, or system service at the same impact or classification level as any live data in use within the pre-production environments.
|
Activity |
Not selected |
NA |
NA |
| SA |
03(03) |
System development lifecycle |
System development lifecycle: Technology refresh
Plan for and implement a technology refresh schedule for the system throughout the system development lifecycle. |
Activity |
Not selected |
NA |
NA |
| SA |
04 |
Acquisition process |
Include the following requirements, descriptions, and criteria, explicitly or by reference, using [Selection (one or more): standardized contract language; [Assignment: organization-defined contract language]] in the acquisition contract for the system, system component, or system service:
- security and privacy functional requirements
- strength of mechanism requirements
- security and privacy assurance requirements
- controls needed to satisfy the security and privacy requirements
- security and privacy documentation requirements
- requirements for protecting security and privacy documentation
- a description of the system development environment and the environment in which the system is intended to operate
- the allocation of responsibility or identification of parties responsible for information security, privacy, and supply chain risk management
- acceptance criteria
|
Control |
Selected |
NA |
NA |
| SA |
04(01) |
Acquisition process |
Acquisition process: Functional properties of controls
Require the developer of the system, system component, or system service to provide a description of the functional properties of the controls to be implemented. |
Control |
Selected |
NA |
NA |
| SA |
04(02) |
Acquisition process |
Acquisition process: Design and implementation information for controls
Require the developer of the system, system component, or system service to provide design and implementation information for the controls that includes: [Selection (one or more): security-relevant external system interfaces; high-level design; low-level design; source code or hardware schematics; [Assignment: organization-defined design and implementation information]] at [Assignment: organization-defined level of detail]. |
Control |
Not selected |
NA |
NA |
| SA |
04(03) |
Acquisition process |
Acquisition process: Development methods, techniques, and practices
Require the developer of the system, system component, or system service to demonstrate the use of a system development lifecycle process that includes:
- [Assignment: organization-defined systems engineering methods]
- [Selection (one or more): [Assignment: organization-defined systems security engineering methods]; [Assignment: organization-defined privacy engineering methods]]
- [Assignment: organization-defined software development methods; testing, evaluation, assessment, verification, and validation methods; and quality control processes]
|
Control |
Not selected |
NA |
NA |
| SA |
04(04) |
Acquisition process |
Acquisition process: Assignment of components to systems
Withdrawn: Incorporated into CM-08(09). |
Control |
NA |
NA |
NA |
| SA |
04(05) |
Acquisition process |
Acquisition process: System, component, and service configurations
Require the developer of the system, system component, or system service to:
- deliver the system, component, or service with [Assignment: organization-defined security configurations] implemented
- use the configurations as the default for any subsequent system, component, or service reinstallation or upgrade
|
Control |
Not selected |
NA |
NA |
| SA |
04(06) |
Acquisition process |
Acquisition process: Use of cyber security products
- Employ only government off-the-shelf or commercial off-the-shelf (COTS) cyber security and cyber security-enabled information technology (IT) products that compose a Cyber Centre-approved solution to protect classified information when the networks used to transmit the information are at a lower classification level than the information being transmitted.
- Ensure that these products have been evaluated or validated by the Cyber Centre or in accordance with Cyber Centre-approved procedures.
|
Control |
Not selected |
NA |
NA |
| SA |
04(07) |
Acquisition process |
Acquisition process: Canadian Common Criteria Program (CCCP)-approved protection profiles
- Limit the use of commercially provided cyber security and cyber security-enabled IT products to those products that have been successfully evaluated against a CCCP-recognized protection profile for a specific technology type, if such a profile exists.
- If no CCCP-recognized protection profile exists for a specific technology type but a commercially provided IT product relies on cryptographic functionality to enforce its security policy, require that the cryptographic module is Federal Information Processing Standard (FIPS)-validated or CCCP-recognized.
|
Control |
Not selected |
NA |
NA |
| SA |
04(08) |
Acquisition process |
Acquisition process: Continuous monitoring plan for controls
Require the developer of the system, system component, or system service to produce a plan for continuous monitoring of control effectiveness that is consistent with the continuous monitoring program of the organization. |
Control |
Not selected |
NA |
NA |
| SA |
04(09) |
Acquisition process |
Acquisition process: Functions, ports, protocols, and services in use
Require the developer of the system, system component, or system service to identify the functions, ports, protocols, and services intended for organizational use. |
Control |
Selected |
NA |
NA |
| SA |
04(10) |
Acquisition process |
Acquisition process: Use of approved digital credential products
Employ only IT products that are recommended by the Cyber Centre for digital credentials capability implemented within organizational systems. |
Control |
Selected |
NA |
NA |
| SA |
04(11) |
Acquisition process |
Acquisition process: System of records
Include [Assignment: organization-defined Privacy Act requirements] in the acquisition contract for the operation of a system of records on behalf of an organization to accomplish an organizational mission or function. |
Control |
Not selected |
NA |
NA |
| SA |
04(12) |
Acquisition process |
Acquisition process: Data ownership
- Include organizational data ownership requirements in the acquisition contract.
- Require all data to be removed from the contractor’s system and returned to the organization within [Assignment: organization-defined time frame].
|
Control |
Selected |
NA |
NA |
| SA |
05 |
System documentation |
- Obtain or develop administrator documentation for the system, system component, or system service that describes:
- secure configuration, installation, and operation of the system, component, or service
- effective use and maintenance of security and privacy functions and mechanisms
- known vulnerabilities regarding configuration and use of administrative or privileged functions
- Obtain or develop user documentation for the system, system component, or system service that describes:
- user-accessible security and privacy functions and mechanisms and how to effectively use those functions and mechanisms
- methods for user interaction, which enable individuals to use the system, component, or service in a more secure manner and protect individual privacy
- user responsibilities in maintaining the security of the system, component, or service and privacy of individuals
- Document attempts to obtain system, system component, or system service documentation when such documentation is either unavailable or non-existent and take [Assignment: organization-defined actions] in response.
- Distribute documentation to [Assignment: organization-defined personnel or roles].
|
Activity |
Selected |
NA |
NA |
| SA |
05(01) |
System documentation |
System documentation: Functional properties of security controls
Withdrawn: Incorporated into SA-04(01). |
NA |
NA |
NA |
NA |
| SA |
05(02) |
System documentation |
System documentation: Security-relevant external system interfaces
Withdrawn: Incorporated into SA-04(02). |
NA |
NA |
NA |
NA |
| SA |
05(03) |
System documentation |
System documentation: High-level design
Withdrawn: Incorporated into SA-04(02). |
NA |
NA |
NA |
NA |
| SA |
05(04) |
System documentation |
System documentation: Low-level design
Withdrawn: Incorporated into SA-04(02). |
NA |
NA |
NA |
NA |
| SA |
05(05) |
System documentation |
System documentation: Source code
Withdrawn: Incorporated into SA-04(02). |
NA |
NA |
NA |
NA |
| SA |
06 |
Software usage restrictions |
Withdrawn: Incorporated into CM-10 and SI-07. |
NA |
NA |
NA |
NA |
| SA |
07 |
User-installed software |
Withdrawn: Incorporated into CM-11 and SI-07. |
NA |
NA |
NA |
NA |
| SA |
08 |
Security and privacy engineering principles |
Apply the following systems security and privacy engineering principles in the specification, design, development, implementation, and modification of the system and system components: [Assignment: organization-defined systems security and privacy engineering principles]. |
Control |
Selected |
NA |
NA |
| SA |
08(01) |
Security and privacy engineering principles |
Security and privacy engineering principles: Clear abstractions
Implement the security design principle of clear abstractions. |
Control |
Not selected |
NA |
NA |
| SA |
08(02) |
Security and privacy engineering principles |
Security and privacy engineering principles: Least common mechanism
Implement the security design principle of least common mechanism in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(03) |
Security and privacy engineering principles |
Security and privacy engineering principles: Modularity and layering
Implement the security design principles of modularity and layering in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(04) |
Security and privacy engineering principles |
Security and privacy engineering principles: Partially ordered dependencies
Implement the security design principle of partially ordered dependencies in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(05) |
Security and privacy engineering principles |
Security and privacy engineering principles: Efficiently mediated access
Implement the security design principle of efficiently mediated access in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(06) |
Security and privacy engineering principles |
Security and privacy engineering principles: Minimized sharing
Implement the security design principle of minimized sharing in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(07) |
Security and privacy engineering principles |
Security and privacy engineering principles: Reduced complexity
Implement the security design principle of reduced complexity in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(08) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure evolvability
Implement the security design principle of secure evolvability in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(09) |
Security and privacy engineering principles |
Security and privacy engineering principles: Trusted components
Implement the security design principle of trusted components in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(10) |
Security and privacy engineering principles |
Security and privacy engineering principles: Hierarchical trust
Implement the security design principle of hierarchical trust in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(11) |
Security and privacy engineering principles |
Security and privacy engineering principles: Inverse modification threshold
Implement the security design principle of inverse modification threshold in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(12) |
Security and privacy engineering principles |
Security and privacy engineering principles: Hierarchical protection
Implement the security design principle of hierarchical protection in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(13) |
Security and privacy engineering principles |
Security and privacy engineering principles: Minimized security elements
Implement the security design principle of minimized security elements in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(14) |
Security and privacy engineering principles |
Security and privacy engineering principles: Least privilege
Implement the security design principle of least privilege in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(15) |
Security and privacy engineering principles |
Security and privacy engineering principles: Predicate permission
Implement the security design principle of predicate permission in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(16) |
Security and privacy engineering principles |
Security and privacy engineering principles: Self-reliant trustworthiness
Implement the security design principle of self-reliant trustworthiness in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(17) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure distributed composition
Implement the security design principle of secure distributed composition in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(18) |
Security and privacy engineering principles |
Security and privacy engineering principles: Trusted communications channels
Implement the security design principle of trusted communications channels in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(19) |
Security and privacy engineering principles |
Security and privacy engineering principles: Continuous protection
Implement the security design principle of continuous protection in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(20) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure metadata management
Implement the security design principle of secure metadata management in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(21) |
Security and privacy engineering principles |
Security and privacy engineering principles: Self-analysis
Implement the security design principle of self-analysis in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(22) |
Security and privacy engineering principles |
Security and privacy engineering principles: Accountability and traceability
Implement the security design principle of accountability and traceability in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(23) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure defaults
Implement the security design principle of secure defaults in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(24) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure failure and recovery
Implement the security design principle of secure failure and recovery in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(25) |
Security and privacy engineering principles |
Security and privacy engineering principles: Economic security
Implement the security design principle of economic security in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(26) |
Security and privacy engineering principles |
Security and privacy engineering principles: Performance security
Implement the security design principle of performance security in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(27) |
Security and privacy engineering principles |
Security and privacy engineering principles: Human factored security
Implement the security design principle of human factored security in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(28) |
Security and privacy engineering principles |
Security and privacy engineering principles: Acceptable security
Implement the security design principle of acceptable security in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(29) |
Security and privacy engineering principles |
Security and privacy engineering principles: Repeatable and documented procedures
Implement the security design principle of repeatable and documented procedures in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(30) |
Security and privacy engineering principles |
Security and privacy engineering principles: Procedural rigour
Implement the security design principle of procedural rigour in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(31) |
Security and privacy engineering principles |
Security and privacy engineering principles: Secure system modification
Implement the security design principle of secure system modification in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(32) |
Security and privacy engineering principles |
Security and privacy engineering principles: Sufficient documentation
Implement the security design principle of sufficient documentation in [Assignment: organization-defined systems or system components]. |
Control |
Not selected |
NA |
NA |
| SA |
08(33) |
Security and privacy engineering principles |
Security and privacy engineering principles: Minimization
Implement the privacy principle of minimization using [Assignment: organization-defined processes]. |
Control |
Not selected |
NA |
NA |
| SA |
08(400) |
Security and privacy engineering principles |
Security and privacy engineering principles: Licensed and certified engineers
Employ licensed and certified security engineers that assume responsibility for the specification, design, development, and implementation of information system security and privacy solutions. |
Control |
Not selected |
NA |
NA |
| SA |
09 |
External system services |
- Require that providers of external system services comply with organizational security and privacy requirements and employ the following controls: [Assignment: organization-defined controls].
- Define and document organizational oversight and user roles and responsibilities with regard to external system services.
- Employ the following processes, methods, and techniques to monitor control compliance by external service providers on an ongoing basis: [Assignment: organization-defined processes, methods, and techniques].
|
Control |
Selected |
NA |
NA |
| SA |
09(01) |
External system services |
External system services: Risk assessments and organizational approvals
- Conduct an organizational risk assessment prior to acquiring or outsourcing information security services.
- Verify that the acquisition or outsourcing of dedicated information security services is approved by [Assignment: organization-defined personnel or roles].
|
Control |
Selected |
NA |
NA |
| SA |
09(02) |
External system services |
External information systems: Identification of functions, ports, protocols, and services
Require providers of the following external system services to identify the functions, ports, protocols, and other services required for the use of such services: [Assignment: organization-defined external system services]. |
Control |
Selected |
NA |
NA |
| SA |
09(03) |
External system services |
External system services: Establish and maintain trust relationship with providers
Establish, document, and maintain trust relationships with external service providers based on the following requirements, properties, factors, or conditions: [Assignment: organization-defined security and privacy requirements, properties, factors, or conditions defining acceptable trust relationships]. |
Control |
Not selected |
NA |
NA |
| SA |
09(04) |
External system services |
External system services: Consistent interests of consumers and providers
Take the following actions to verify that the interests of [Assignment: organization-defined external service providers] are consistent with and reflect organizational interests: [Assignment: organization-defined actions]. |
Control |
Not selected |
NA |
NA |
| SA |
09(05) |
External system services |
External system services: Processing, storage, and service location
Restrict the location of [Selection (one or more): information processing; information or data; system services] to [Assignment: organization-defined locations] based on [Assignment: organization-defined requirements or conditions]. |
Control |
Not selected |
NA |
NA |
| SA |
09(06) |
External system services |
External system services: Organization-controlled cryptographic keys
Maintain exclusive control of cryptographic keys for encrypted material stored or transmitted through an external system. |
Control |
Not selected |
NA |
NA |
| SA |
09(07) |
External system services |
External system services: Organization-controlled integrity checking
Provide the capability to check the integrity of information while it resides in the external system. |
Control |
Not selected |
NA |
NA |
| SA |
09(08) |
External system services |
External system services: Processing and storage location — within Canada
Restrict the geographic location of information processing and data storage to facilities located within in the legal jurisdictional boundary of Canada. |
Control |
Selected |
NA |
NA |
| SA |
10 |
Developer configuration management |
Require the developer of the system, system component, or system service to:
- perform configuration management during system, component, or service [Selection (one or more): design; development; implementation; operation; disposal]
- document, manage, and control the integrity of changes to [Assignment: organization-defined configuration items under configuration management]
- implement only organization-approved changes to the system, component, or service
- document approved changes to the system, component, or service and the potential security and privacy impacts of such changes
- track security flaws and flaw resolution within the system, component, or service and report findings to [Assignment: organization-defined personnel]
|
Activity |
Selected |
NA |
NA |
| SA |
10(01) |
Developer configuration management |
Developer configuration management: Software and firmware integrity verification
Require the developer of the system, system component, or system service to enable integrity verification of software and firmware components. |
Activity |
Selected |
NA |
NA |
| SA |
10(02) |
Developer configuration management |
Developer configuration management: Alternative configuration management processes
Provide an alternate configuration management process using organizational personnel in the absence of a dedicated developer configuration management team. |
Activity |
Not selected |
NA |
NA |
| SA |
10(03) |
Developer configuration management |
Developer configuration management: Hardware integrity verification
Require the developer of the system, system component, or system service to enable integrity verification of hardware components. |
Activity |
Not selected |
NA |
NA |
| SA |
10(04) |
Developer configuration management |
Developer configuration management: Trusted generation
Require the developer of the system, system component, or system service to employ tools for comparing newly generated versions of security-relevant hardware descriptions, source code, and object code with previous versions. |
Activity |
Not selected |
NA |
NA |
| SA |
10(05) |
Developer configuration management |
Developer configuration management: Mapping integrity for version control
Require the developer of the system, system component, or system service to maintain the integrity of the mapping between the master build data describing the current version of security-relevant hardware, software, and firmware and the on-site master copy of the data for the current version. |
Activity |
Not selected |
NA |
NA |
| SA |
10(06) |
Developer configuration management |
Developer configuration management: Trusted distribution
Require the developer of the system, system component, or system service to execute procedures for ensuring that security-relevant hardware, software, and firmware updates distributed to the organization are exactly as specified by the master copies. |
Activity |
Not selected |
NA |
NA |
| SA |
10(07) |
Developer configuration management |
Developer configuration management: Security and privacy representatives
Require [Assignment: organization-defined security and privacy representatives] to be included in the [Assignment: organization-defined configuration change management and control process]. |
Activity |
Selected |
1 [SSC, TBS and Cyber Centre]
2 [SSC projects and services serving multiple departments] |
NA |
| SA |
11 |
Developer testing and evaluation |
At all post-design stages of the system development lifecycle, require the developer of the system, system component, or system service to:
- develop and implement a plan for ongoing security and privacy control assessments
- perform [Selection (one or more): unit; integration; system; regression] testing/evaluation [Assignment: organization-defined frequency] at [Assignment: organization-defined depth and coverage]
- produce evidence of the execution of the assessment plan and the results of the testing and evaluation
- implement a verifiable flaw remediation process
- correct flaws identified during testing and evaluation
|
Activity |
Selected |
NA |
NA |
| SA |
11(01) |
Developer testing and evaluation |
Developer testing and evaluation: Static code analysis
Require the developer of the system, system component, or system service to employ static code analysis tools to identify common flaws and document the results of the analysis. |
Activity |
Not selected |
NA |
NA |
| SA |
11(02) |
Developer testing and evaluation |
Developer testing and evaluation: Threat modeling and vulnerability analyses
Require the developer of the system, system component, or system service to perform threat modelling and vulnerability analyses during development and the subsequent testing and evaluation of the system, component, or service that:
- uses the following contextual information: [Assignment: organization-defined information concerning impact, environment of operations, known or assumed threats, and acceptable risk levels]
- employs the following tools and methods: [Assignment: organization-defined tools and methods]
- conducts the modelling and analyses at the following level of rigour: [Assignment: organization-defined breadth and depth of modelling and analyses]
- produces evidence that meets the following acceptance criteria: [Assignment: organization-defined acceptance criteria]
|
Activity |
Not selected |
NA |
NA |
| SA |
11(03) |
Developer testing and evaluation |
Developer testing and evaluation: Independent verification of assessment plans and evidence
- Require an independent agent satisfying [Assignment: organization-defined independence criteria] to verify the correct implementation of the developer security and privacy assessment plans and the evidence produced during testing and evaluation.
- Verify that the independent agent is provided with sufficient information to complete the verification process or granted the authority to obtain such information.
|
Activity |
Not selected |
NA |
NA |
| SA |
11(04) |
Developer testing and evaluation |
Developer testing and evaluation: Manual code reviews
Require the developer of the system, system component, or system service to perform a manual code review of [Assignment: organization-defined specific code] using the following processes, procedures, and/or techniques: [Assignment: organization-defined processes, procedures, and/or techniques]. |
Activity |
Not selected |
NA |
NA |
| SA |
11(05) |
Developer testing and evaluation |
Developer testing and evaluation: Penetration testing
Require the developer of the system, system component, or system service to perform penetration testing:
- at the following level of rigour: [Assignment: organization-defined breadth and depth of testing]
- under the following constraints: [Assignment: organization-defined constraints]
|
Activity |
Not selected |
NA |
NA |
| SA |
11(06) |
Developer testing and evaluation |
Developer testing and evaluation: Attack surface reviews
Require the developer of the system, system component, or system service to perform attack surface reviews. |
Activity |
Not selected |
NA |
NA |
| SA |
11(07) |
Developer testing and evaluation |
Developer testing and evaluation: Verify scope of testing and evaluation
Require the developer of the system, system component, or system service to verify that the scope of testing and evaluation provides complete coverage of the required controls at the following level of rigour: [Assignment: organization-defined breadth and depth of testing and evaluation]. |
Activity |
Not selected |
NA |
NA |
| SA |
11(08) |
Developer testing and evaluation |
Developer testing and evaluation: Dynamic code analysis
Require the developer of the system, system component, or system service to employ dynamic code analysis tools to identify common flaws and document the results of the analysis. |
Activity |
Not selected |
NA |
NA |
| SA |
11(09) |
Developer testing and evaluation |
Developer testing and evaluation: Interactive application security testing
Require the developer of the system, system component, or system service to employ interactive application security testing tools to identify flaws and document the results. |
Activity |
Not selected |
NA |
NA |
| SA |
12 |
Supply chain protection |
Withdrawn: Moved to SR Family. |
NA |
NA |
NA |
NA |
| SA |
12(01) |
Supply chain protection |
Supply chain protection: Acquisition strategies / tools / methods
Withdrawn: Moved to SR-05. |
NA |
NA |
NA |
NA |
| SA |
12(02) |
Supply chain protection |
Supply chain protection: Supplier reviews
Withdrawn: Moved to SR-06. |
NA |
NA |
NA |
NA |
| SA |
12(03) |
Supply chain protection |
Supply chain protection: Trusted shipping and warehousing
Withdrawn: Incorporated into SR-03. |
NA |
NA |
NA |
NA |
| SA |
12(04) |
Supply chain protection |
Supply chain protection: Diversity of suppliers
Withdrawn: Incorporated into SR-03(01). |
NA |
NA |
NA |
NA |
| SA |
12(05) |
Supply chain protection |
Supply chain protection: Limitation of harm
Withdrawn: Incorporated into SR-03(02). |
NA |
NA |
NA |
NA |
| SA |
12(06) |
Supply chain protection |
Supply chain protection: Minimizing procurement time
Withdrawn: Incorporated into SR-05(01). |
NA |
NA |
NA |
NA |
| SA |
12(07) |
Supply chain protection |
Supply chain protection: Assessments prior to selection / acceptance / update
Withdrawn: Moved to SR-05(02). |
NA |
NA |
NA |
NA |
| SA |
12(08) |
Supply chain protection |
Supply chain protection: Use of all-source intelligence
Withdrawn: Incorporated into RA-03(02). |
NA |
NA |
NA |
NA |
| SA |
12(09) |
Supply chain protection |
Supply chain protection: Operations security
Withdrawn: Moved to SR-07. |
NA |
NA |
NA |
NA |
| SA |
12(10) |
Supply chain protection |
Supply chain protection: Validate as genuine and not altered
Withdrawn: Moved to SR-04(03). |
NA |
NA |
NA |
NA |
| SA |
12(11) |
Supply chain protection |
Supply chain protection: Penetration testing / analysis of elements, processes, and actors
Withdrawn: Moved to SR-06(01). |
NA |
NA |
NA |
NA |
| SA |
12(12) |
Supply chain protection |
Supply chain protection: Inter-organizational agreements
Withdrawn: Moved to SR-08. |
NA |
NA |
NA |
NA |
| SA |
12(13) |
Supply chain protection |
Supply chain protection: Critical information system components
Withdrawn: Incorporated into MA-06 and RA-09. |
NA |
NA |
NA |
NA |
| SA |
12(14) |
Supply chain protection |
Supply chain protection: Identity and traceability
Withdrawn: Moved to SR-04(01) and SR-04(02). |
NA |
NA |
NA |
NA |
| SA |
12(15) |
Supply chain protection |
Supply chain protection: Processes to address weaknesses or deficiencies
Withdrawn: Incorporated into SR-03. |
NA |
NA |
NA |
NA |
| SA |
13 |
Trustworthiness |
Withdrawn: Incorporated into SA-08. |
NA |
NA |
NA |
NA |
| SA |
14 |
Criticality analysis |
Withdrawn: Incorporated into RA-09. |
NA |
NA |
NA |
NA |
| SA |
14(01) |
Criticality analysis |
Criticality analysis: Critical components with no viable alternative sourcing
Withdrawn: Incorporated into SA-20. |
NA |
NA |
NA |
NA |
| SA |
15 |
Development process, standards, and tool |
- Require the developer of the system, system component, or system service to follow a documented development process that:
- explicitly addresses security and privacy requirements
- identifies the standards and tools used in the development process
- documents the specific tool options and tool configurations used in the development process
- documents, manages, and ensures the integrity of changes to the process and/or tools used in development
- Review the development process, standards, tools, tool options, and tool configurations [Assignment: organization-defined frequency] to determine if the process, standards, tools, tool options, and tool configurations selected and employed can satisfy the following security and privacy requirements: [Assignment: organization-defined security and privacy requirements].
|
Activity |
Selected |
NA |
NA |
| SA |
15(01) |
Development process, standards, and tool |
Development process, standards, and tools: Quality metrics
Require the developer of the system, system component, or system service to:
- define quality metrics at the beginning of the development process
- provide evidence of meeting the quality metrics [Selection (one or more): [Assignment: organization-defined frequency]; [Assignment: organization-defined program review milestones]; upon delivery]
|
Activity |
Not selected |
NA |
NA |
| SA |
15(02) |
Development process, standards, and tool |
Development process, standards, and tools: Security and privacy control traceability tools
Require the developer of the system, system component, or system service to select and employ security and privacy controls traceability tools for use during the development process. |
Activity |
Not selected |
NA |
NA |
| SA |
15(03) |
Development process, standards, and tool |
Development process, standards, and tools: Criticality analysis
Require the developer of the system, system component, or system service to perform a criticality analysis:
- at the following decision points in the system development lifecycle: [Assignment: organization-defined decision points in the system development lifecycle]
- at the following level of rigour: [Assignment: organization-defined breadth and depth of criticality analysis]
|
Activity |
Selected |
NA |
NA |
| SA |
15(04) |
Development process, standards, and tool |
Development process, standards, and tools: Threat modeling / vulnerability analysis
Withdrawn: Incorporated into SA-11(02). |
NA |
NA |
NA |
NA |
| SA |
15(05) |
Development process, standards, and tool |
Development process, standards, and tools: Attack surface reduction
Require the developer of the system, system component, or system service to reduce attack surfaces to [Assignment: organization-defined thresholds]. |
Activity |
Not selected |
NA |
NA |
| SA |
15(06) |
Development process, standards, and tool |
Development process, standards, and tools: Continuous improvement
Require the developer of the system, system component, or system service to implement an explicit process to continuously improve the development process. |
Activity |
Not selected |
NA |
NA |
| SA |
15(07) |
Development process, standards, and tool |
Development process, standards, and tools: Automated vulnerability analysis
Require the developer of the system, system component, or system service [Assignment: organization-defined frequency] to:
- perform an automated vulnerability analysis using [Assignment: organization-defined tools]
- determine the exploitation potential for discovered vulnerabilities
- determine potential risk mitigations for delivered vulnerabilities
- deliver the outputs of the tools and results of the analysis to [Assignment: organization-defined personnel or roles]
|
Activity |
Not selected |
NA |
NA |
| SA |
15(08) |
Development process, standards, and tool |
Development process, standards, and tools: Reuse of threat and vulnerability information
Require the developer of the system, system component, or system service to use threat modeling and vulnerability analyses from similar systems, components, or services to inform the current development process. |
Activity |
Not selected |
NA |
NA |
| SA |
15(09) |
Development process, standards, and tool |
Development process, standards, and tools: Use of live data Withdrawn: Incorporated into SA-03(02). |
NA |
NA |
NA |
NA |
| SA |
15(10) |
Development process, standards, and tool |
Development process, standards, and tools: Incident response plan
Require the developer of the system, system component, or system service to provide, implement, and test an incident response plan. |
Activity |
Not selected |
NA |
NA |
| SA |
15(11) |
Development process, standards, and tool |
Development process, standards, and tools: Archive system or component
Require the developer of the system or system component to archive the system or component to be released or delivered together with the corresponding evidence supporting the final security and privacy review. |
Activity |
Not selected |
NA |
NA |
| SA |
15(12) |
Development process, standards, and tool |
Development process, standards, and tool: Minimize personal information
Require the developer of the system or system component to minimize the use of personal information in development and test environments. |
Activity |
Not selected |
NA |
NA |
| SA |
16 |
Developer provided training |
Require the developer of the system, system component, or system service to provide the following training on the correct use and operation of the implemented security and privacy functions, controls, and/or mechanisms: [Assignment: organization-defined training]. |
Control |
Selected |
NA |
NA |
| SA |
17 |
Developer security and privacy architecture and design |
Require the developer of the system, system component, or system service to produce a design specification and security and privacy architecture that:
- is consistent with the organization’s security and privacy architecture that is an integral part the organization’s enterprise architecture
- accurately and completely describes the required security and privacy functionality and the allocation of controls among physical and logical components
- expresses how individual security and privacy functions, mechanisms, and services work together to provide required security and privacy capabilities and a unified approach to protection
|
Activity |
Selected |
NA |
NA |
| SA |
17(01) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Formal policy model
Require the developer of the system, system component, or system service to:
- produce, as an integral part of the development process, a formal policy model describing the [Assignment: organization-defined elements of organizational security and privacy policy] to be enforced
- prove that the formal policy model is internally consistent and sufficient to enforce the defined elements of the organizational security and privacy policy when implemented
|
Activity |
Not selected |
NA |
NA |
| SA |
17(02) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Security-relevant components
Require the developer of the system, system component, or system service to:
- define security-relevant hardware, software, and firmware
- provide a rationale that the definition for security-relevant hardware, software, and firmware is complete
|
Activity |
Not selected |
NA |
NA |
| SA |
17(03) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Formal correspondence
Require the developer of the system, system component, or system service to:
- produce, as an integral part of the development process, a formal top-level specification that specifies the interfaces to security-relevant hardware, software, and firmware in terms of exceptions, error messages, and effects
- show, via proof to the extent feasible with additional informal demonstration as necessary, that the formal top-level specification is consistent with the formal policy model
- show, via informal demonstration, that the formal top-level specification completely covers the interfaces to security-relevant hardware, software, and firmware
- show that the formal top-level specification is an accurate description of the implemented security-relevant hardware, software, and firmware
- describe the security-relevant hardware, software, and firmware mechanisms not addressed in the formal top-level specification but strictly internal to the security-relevant hardware, software, and firmware
|
Activity |
Not selected |
NA |
NA |
| SA |
17(04) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Informal correspondence
Require the developer of the system, system component, or system service to:
- produce, as an integral part of the development process, an informal descriptive top-level specification that specifies the interfaces to security-relevant hardware, software, and firmware in terms of exceptions, error messages, and effects
- show, via [Selection (one): informal demonstration; convincing argument with formal methods as feasible], that the descriptive top-level specification is consistent with the formal policy model
- show, via informal demonstration, that the descriptive top-level specification completely covers the interfaces to security-relevant hardware, software, and firmware
- show that the descriptive top-level specification is an accurate description of the interfaces to security-relevant hardware, software, and firmware
- describe the security-relevant hardware, software, and firmware mechanisms not addressed in the descriptive top-level specification but strictly internal to the security-relevant hardware, software, and firmware
|
Activity |
Not selected |
NA |
NA |
| SA |
17(05) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Conceptually simple design
Require the developer of the system, system component, or system service to:
- design and structure the security-relevant hardware, software, and firmware to use a complete, conceptually simple protection mechanism with precisely defined semantics
- internally structure the security-relevant hardware, software, and firmware with specific regard for this mechanism
|
Activity |
Not selected |
NA |
NA |
| SA |
17(06) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Structure for testing
Require the developer of the system, system component, or system service to structure security-relevant hardware, software, and firmware to facilitate testing. |
Activity |
Not selected |
NA |
NA |
| SA |
17(07) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Structure for least privilege
Require the developer of the system, system component, or system service to structure security-relevant hardware, software, and firmware to facilitate controlling access with least privilege. |
Activity |
Not selected |
NA |
NA |
| SA |
17(08) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Orchestration
Design [Assignment: organization-defined critical systems or system components] with coordinated behaviour to implement the following capabilities: [Assignment: organization-defined capabilities, by system or component]. |
Activity |
Not selected |
NA |
NA |
| SA |
17(09) |
Developer security and privacy architecture and design |
Developer security and privacy architecture and design: Design diversity
Use different designs for [Assignment: organization-defined critical systems or system components] to satisfy a common set of requirements or to provide equivalent functionality. |
Activity |
Not selected |
NA |
NA |
| SA |
18 |
Tamper resistance and detection |
Withdrawn: Moved to SR-09. |
NA |
NA |
NA |
NA |
| SA |
18(01) |
Tamper resistance and detection |
Tamper resistance and detection: Multiple phases of SDLC
Withdrawn: Moved to SR-09(01). |
NA |
NA |
NA |
NA |
| SA |
18(02) |
Tamper resistance and detection |
Tamper resistance and detection: Inspection of information systems, components, or devices
Withdrawn: Moved to SR-10. |
NA |
NA |
NA |
NA |
| SA |
19 |
Component authenticity |
Withdrawn: Moved to SR-11. |
NA |
NA |
NA |
NA |
| SA |
19(01) |
Component authenticity |
Component authenticity: Anti-counterfeit training
Withdrawn: Moved to SR-11(01). |
NA |
NA |
NA |
NA |
| SA |
19(02) |
Component authenticity |
Component authenticity: Configuration control for component service / repair
Withdrawn: Moved to SR-11(02). |
NA |
NA |
NA |
NA |
| SA |
19(03) |
Component authenticity |
Component authenticity: Component disposal
Withdrawn: Moved to SR-12. |
NA |
NA |
NA |
NA |
| SA |
19(04) |
Component authenticity |
Component authenticity: Anti-counterfeit scanning
Withdrawn: Moved to SR-11(03). |
NA |
NA |
NA |
NA |
| SA |
20 |
Customized development of critical components |
Reimplement or custom develop the following critical system components: [Assignment: organization-defined critical system components]. |
Control |
Not selected |
NA |
NA |
| SA |
21 |
Developer screening |
Require that the developer of [Assignment: organization-defined system, system component, or system service]:
- has appropriate access authorizations as determined by assigned [Assignment: organization-defined official government duties]
- satisfies the following additional personnel screening criteria: [Assignment: organization-defined additional personnel screening criteria]
|
Control |
Not selected |
NA |
NA |
| SA |
21(01) |
Developer screening |
Developer screening: Validation of screening
Withdrawn: Incorporated into SA-21. |
NA |
NA |
NA |
NA |
| SA |
22 |
Unsupported system components |
- Replace system components when support for the components is no longer available from the developer, vendor, or manufacturer.
- Provide the following options for alternative sources for continued support for unsupported components [Selection (one or more): in-house support; [Assignment: organization-defined support from external providers]].
|
Control |
Selected |
NA |
NA |
| SA |
22(01) |
Unsupported system components |
Unsupported system components: Alternative sources for continued support
Withdrawn: Incorporated into SA-22. |
NA |
NA |
NA |
NA |
| SA |
23 |
Specialization |
Employ [Selection (one or more): design; modification; augmentation; reconfiguration] on [Assignment: organization-defined systems or system components] supporting mission-essential services or functions to increase the robustness in those systems or components. |
Activity |
Not selected |
NA |
NA |
| SA |
400 |
Sovereignty and jurisdiction |
Require the organizational business function to conduct a sovereignty and jurisdiction threat and risk assessment process at the [Selection (one or more): organization-level, mission/business-level, system-level] that:
- conducts an injury assessment to determine the maximum potential injuries that may be suffered due to external legal compulsion of the business functions or information assets by:
- considering the business needs for security including any laws or regulations which require that data not be disclosed or compromised
- updating the security categorization of the business functions or information assets
- documenting the negative consequences of legal compulsion
- performs jurisdiction-specific threat assessment that establishes a likelihood of being targeted
- undertakes a vulnerability assessment to evaluate the potential means by which the external jurisdiction could exploit the business functions or information assets
- completes a jurisdiction-specific risk assessment
|
Control |
Selected |
NA |
NA |
| SA |
400(01) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Threat and risk assessment
Require the organization to perform threat and risk assessments in relation to data sovereignty, considering its jurisdiction and by which surfaces legal compulsion may be effective. |
Control |
Not selected |
NA |
NA |
| SA |
400(02) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Legal and contractual assessment
Require the organization to perform threat and risk assessments in relation to data sovereignty, considering its jurisdiction and by which surfaces legal compulsion may be effective. |
Control |
Not selected |
NA |
NA |
| SA |
400(03) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Business process attribute marking
Ensure business processes receive the intended handling with respect to legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(04) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Protection of data at rest
Prevent data from residing in any other legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(05) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Protection of data in transit
Prevent data from transiting through any other legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(06) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Protection of data in use
Prevent data from being used in any other legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(07) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Protection against extraterritorial compulsion
Prevent business functions from being compromised by individuals or corporations that are being compelled by a different legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(08) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Protection of business lifecycle
Prevent business functions from being compromised by lifecycle attacks embedded via legal compulsion in or from a different legal jurisdiction. |
Control |
Not selected |
NA |
NA |
| SA |
400(09) |
Sovereignty and jurisdiction |
Sovereignty and jurisdiction: Public ownership
Prevent business functions from being compromised by ownership transfer of lifecycle functions to a different legal jurisdiction. |
Control |
Not selected |
NA |
NA |